Reflections on Project Haiku: Accounts and Ownership
This is part of a series of posts I’m writing to put down my thoughts on the recently retired Mozilla Connected Devices Haiku project. By focusing on the user problem and not the business model, we quickly determined that we wanted as little data from our users as we could get away with. For context and an overview of the project, please see my earlier post.
When I was a kid, my brothers and I had wired walkie-talkies. Intercoms really. Each unit was attached with about 100’ of copper wire. One could be downstairs and with the wire trailed dangerously under doors and up stairs we could communicate between kitchen and bedroom. Later, in order to talk with a friend in the appartment block opposite us, we got a string pulled taut between our two balconies. With tin cans on each end of the string, you could just about hear what the other was saying.
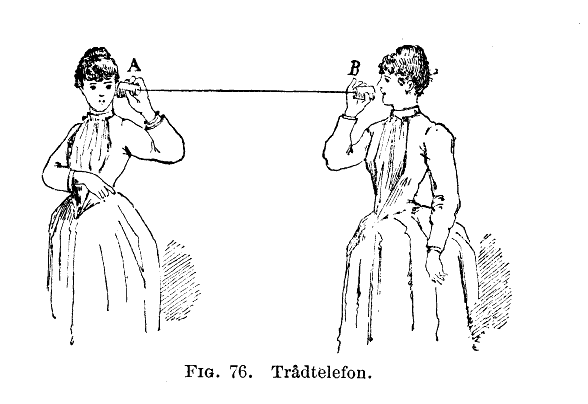
RF-based wireless communication had existed for a long time already, but I bring these specific communication examples up because the connection we made was exclusive and private.
We didn’t need to agree on a frequency and hope no-one else was listening in. The devices didn’t just enable the connection, they were the connection. We didn’t sign up for a service, didn’t pay any subscription, and when we tired of it and it was given away, no contracts needed to be amended; the new owners simply picked up each end and started their own direct and private conversation. In Project Haiki, when we thought about IoT and connecting people, this was the analogy we adopted.
That doesnt sound like a very radical position to take. But look around you and some of the ways you communicate with friends and loved ones today when you are physically apart. Cellular/SMS, Facebook, Skype, Facetime, Twitter, WhatsApp, Telegram… In each and every case you have accounts and arrangement with companies to make communication possible. And in each case that company can log at least the metadata if not the content of your conversations, change terms of agreement and policies, raise prices, or terminate the agreement entirely and disconnect you. They can be subpoena’d for their records and may even be obliged by law to retain and hand over data with their customers transactions. In our tin can and string analogy, there’s a large, locked black junction box sitting between you and your friend. You may own the equipment you use on your end, but it can be rendered effectively useless or even intrusive and hostile at any time, and there’s probably not a thing you can do about it. Everything about this situation is wrong for the direct, personal and private channel we wanted to establish to let kids and grandparent share moments and be a part of each others lives from a distance.
Clearly, some parts of this problem are more tractable than others. We’re not in the ISP business for example; how you get to the internet is outside our control. But, keeping this analogy in mind provided a north star for our project. Whenever we were faced with a decision to make, it helped steer us. So when we thought about the unboxing and setup experience, we asked ourselves, “Do we actually need user accounts for these people?”
Here’s the typical scenario when you install an app or take delivery of some shiny new tech. You plug it in or fire it up for the first time and you are asked to login or sign up. You create a new account with company X, providing your name, address, email, maybe gender or age bracket, perhaps they want categories of interest, and an agreement to be spammed. If its a paid service, they’ll want your credit card info too. Furthermore, the app then requests a set of permissions giving it access to your address book. Remember, the goal here is to allow a kid and their grandparent to exchange messages and chat from time to time. Which of these do we as Mozilla - the service provider - actually need?
Name? These two people are already in touch, so they don’t need to find each other in a directory. Their invitations to connect/pair could take the form of a URL sent via text, or a QR code printed and sent via snail mail. These devices only connect these two people so we don’t have to identify who a message is from. And even if we did want that, they can configure it and send it from the device itself. We don’t really need to store their names.
Address? Why would we care? We don’t need to send them anything. If they do need to replace a device, they can provide a shipping address at that time.
Email? Most companies want to maintain a relationship with their customers. They’ll email news of other services, offers of upgrades from time to time. Its called customer engagement and that database of email addresses is one of a company’s key assets. What if we didn’t do that?
What if we treated this product just like the tin cans, or the intercom or any other thing you might purchase from a store. There’s a single transaction to acquire the thing, and that’s it. In this scenario, we only care about the device itself, its owned and used by whoever has it, and they can transfer it or sell it on and we don’t need to know or care. In our grandparent/grandchild scenario, as one child grows up, maybe they pass it on to a younger sibling. Or gift it to another family. All the users need is a way to break the “connection” that ties their devices together, and a way to start over with the invitation-to-connect process. The device itself needs to be uniquely identified to facilitate this, but not the user.
How this would shake out is one of the things we’ll have to wait on, now that Project Haiku is on hold. Would it really have been practical to run a service like this with no visibility into who was using it? Would we be able to run the service at a low enough cost to allow us to support those devices indefinitely? Would this proposition have been understood and embraced by the market? The anonymity and opacity works both ways: we cant retrieve message histories for users, we can’t restore lost connections from the server side. If a device was stolen or even just picked up by a sibling, we can’t filter or block connections and nuisance messages. Each connected/paired device can sever that pairing, but as long as they are connected, any message between the two is legitimate by definition.
We’ve grown accustomed to the need for user accounts, and for some part of our relationships to be owned and gated by 3rd parties we maintain agreements with. If Project Haiku and its aspirations can serve to question these assumptions and provide some food for thought, it was time well spent.